Authors:
Jennifer Whitson
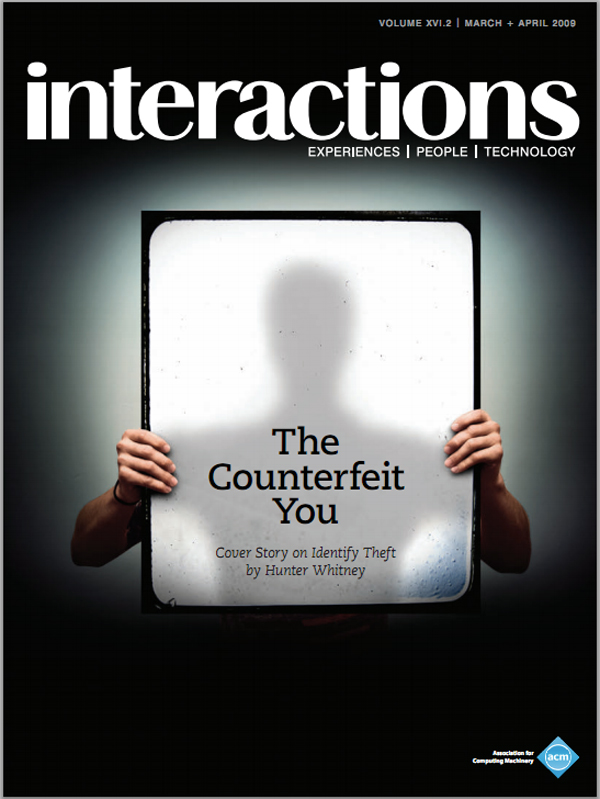
Several recent high-profile incidents have thrust identity theft into the media spotlight. The first to gain notoriety involved the credit-verification company ChoicePoint, which in 2004 inadvertently delivered electronic files containing the names, addresses, social security numbers, and credit reports for almost 140,000 people to identity thieves in the Los Angeles area. In 2007 the British government lost computer disks that contained the personal details of every family in the country. In both cases, the media and authorities articulated a series of anxieties about how this data could be exploited. A plethora of security experts quickly emerged to offer citizens…
You must be a member of SIGCHI, a subscriber to ACM's Digital Library, or an interactions subscriber to read the full text of this article.
GET ACCESS
Join ACM SIGCHIIn addition to all of the professional benefits of being a SIGCHI member, members get full access to interactions online content and receive the print version of the magazine bimonthly.
Subscribe to the ACM Digital Library
Get access to all interactions content online and the entire archive of ACM publications dating back to 1954. (Please check with your institution to see if it already has a subscription.)
Subscribe to interactions
Get full access to interactions online content and receive the print version of the magazine bimonthly.






Post Comment
No Comments Found